Wireguard, macOS, and Linux Virtual Machines
06 October, 2018
(The primary material for this blog post was released on github. I'm reproducing part it here as a blog post.)Over the long term, the Wireguard VPN is set to send shockwaves through the VPN community with its modern cryptographic design, performance, stealthiness against active network scanners, and commitment to security through a minimally complex code base. It is my belief that these characteristics firmly place Wireguard among the best VPN options available. Over time, it is likely that commercial solutions will be developed around Wireguard similarly to commercial wrappers around OpenVPN.
This repository is dedicated to deploying a Wireguard VPN on macOS via a Linux VM running under a virtualization solution such as Parallels. There are many alternatives to this approach - including omitting the Linux piece altogether and using the cross-platform macOS Wireguard tools - but I'm interested in using the Wireguard kernel module from a Mac. This has to be done from a Linux VM or container, and we'll talk about the VM route in this write up.
The primary use case for running such a VPN solution is to provide security for network traffic emanating from a Mac laptop that is connected to a potentially hostile wireless network. This includes the network at the local coffee shop among many others. Nothing against coffee shops of course (I love coffee), but they are in the business of making wonderful caffeinated potions - not hardening their network infrastructure against adversaries. In terms of general threats to network traffic, a properly deployed VPN allows you to shift much of the security burden to the other side of the VPN. In this case, the remote Wireguard end point will be deployed in a major cloud provider or ISP network. The security of, say, Google's GCE network or Amazon's AWS network is far higher than the network of the local coffee shop.
Note macOS security is a broad topic, and this repository is meant only to discuss a VPN solution based on Wireguard. For a comprehensive treatment of macOS security, including other VPN options, see the excellent macOS Security and Privacy Guide.
Prerequisites
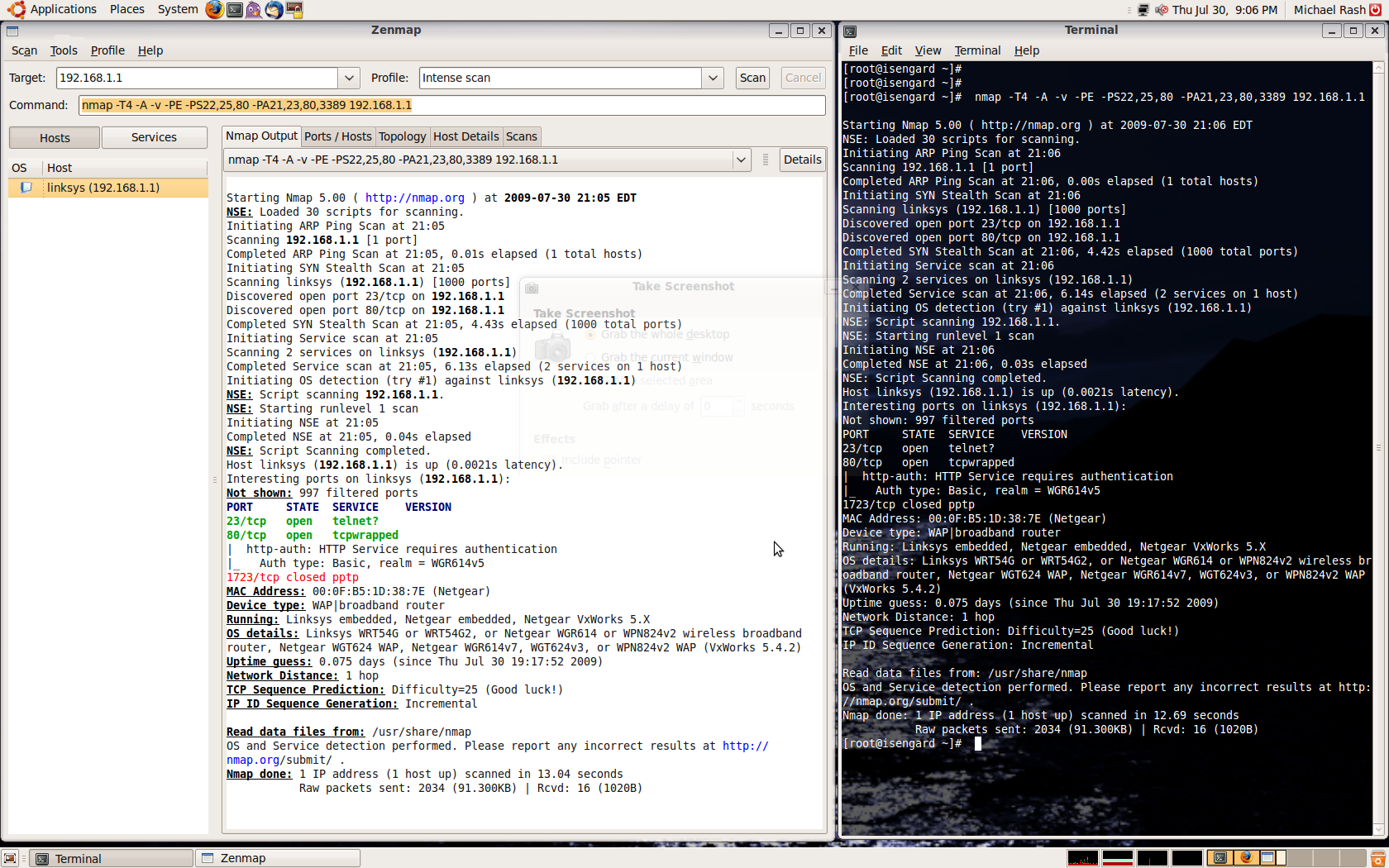
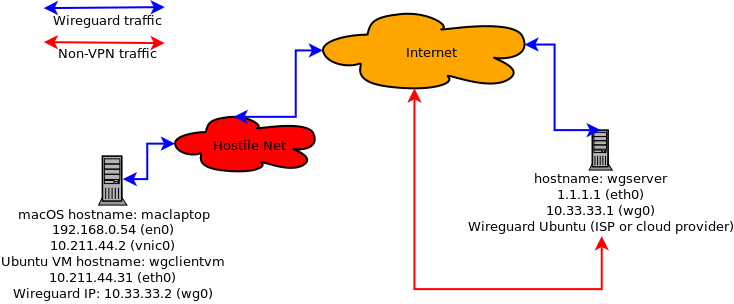
To fully implement Wireguard in this manner, we'll assume the following:- An Ubuntu Linux VM is running under Parallels on a Mac laptop. Wireguard will run from this VM, and will constitute the "client" side of the VPN.
- The Mac laptop will be connected wirelessly to the network at the local coffee shop, and have an IP assigned via DHCP as usual.
- The "server" side of the Wireguard VPN is an Ubuntu system running on a major cloud provider with an Internet-facing IP address.
- Wireguard has been [installed](https://www.wireguard.com/install/) on both Ubuntu VM's, and key pairs have been [generated and shared](https://www.wireguard.com/quickstart/).
- Wireguard client - Mac laptop hostname and IP addresses:
- Mac laptop hostname: maclaptop
- Mac laptop wireless IP on the coffee shop network: 192.168.0.54, interface: en0
- Mac laptop virtual NIC IP (under Parallels): 10.211.44.2, interface: vnic0
- Mac laptop Ubuntu VM Wireguard hostname: wgclientvm, IP: 10.211.44.31
- Mac laptop Ubuntu VM Wireguard IP: 10.33.33.2, interface: wg0
- Wireguard server - Ubuntu system hostname and IP addresses:
- Hostname: wgserver
- IP: 1.1.1.1, interface: eth0
- Wireguard IP: 10.33.33.1, interface: wg0
 For the remainder of the writeup, head on over to the
github repository.
For the remainder of the writeup, head on over to the
github repository.
 Recently a
Recently a